The Enterprise OPA Platform
The developer-friendly, fine-grained authorization platform trusted by enterprises around the world.
Frequently Asked Questions
Do I have to talk to a salesperson?
The Enterprise OPA Platform can be provisioned for you within minutes after a short intro from our experts.
We’ll just quickly need to understand the size and types of your deployment before we can set up, to make sure you have everything you need right away.
What is OPA and how does it relate to Styra DAS?
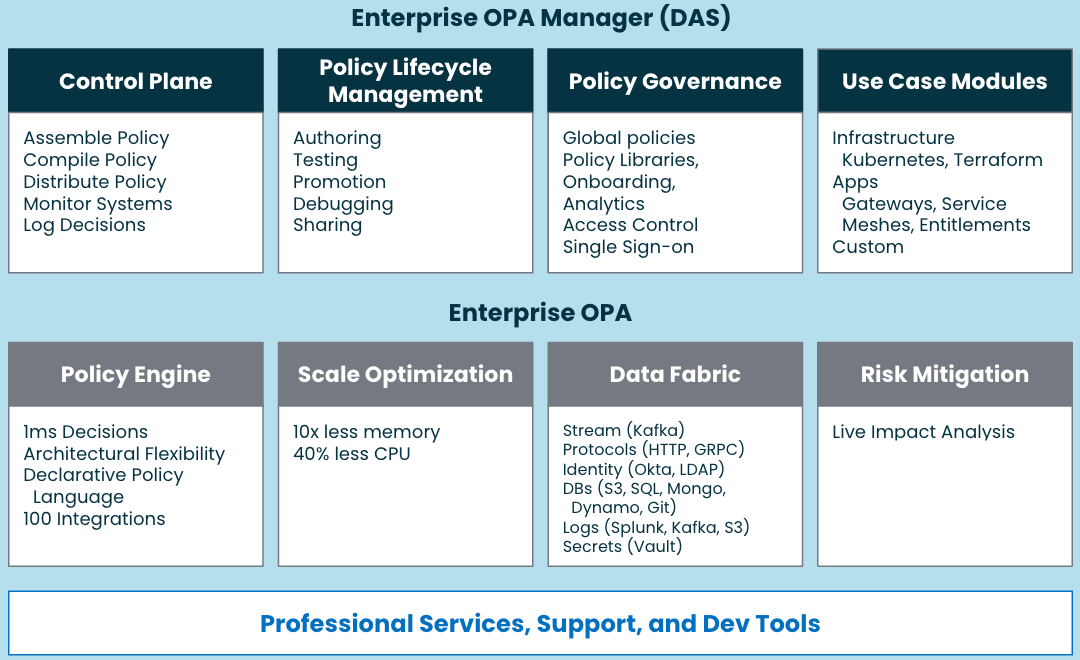
Open Policy Agent (OPA) is the cloud-native computing foundation project Styra founded to provide unified authorization across the cloud-native stack. Styra Declarative Authorization Service (DAS) is the control plane/management plane for OPA. It provides a single pane of glass for policy authoring, distribution, impact analysis, monitoring and auditing. They’re like PB&J—they go great together!
Where does OPA run and how does it communicate with Styra DAS?
Styra DAS is the control plane for OPA. You run OPA wherever you want and then connect it to Styra DAS as its management/control plane. For all communication, OPA reaches out to Styra DAS over HTTPS and authenticates with a bearer token. (Of course, all of this is automatically configured for you, with simple installation instructions in Styra DAS!)
Where can I learn more about policy authoring with OPA?
Styra DAS has 1000+ policies built right in, so you can get started in minutes—there’s even a number of quick starts to walk you through setting up your first policies across systems if you like.
If you want to dive deeper and understand how to build fully custom policies with Open Policy Agent, then Styra academy is what you’re looking for! We’ve built out lots of great lessons on OPA, and its policy language Rego—directly from Styra, the folks who invented it!
How many systems does Styra DAS Enterprise support?
Styra DAS Enterprise supports an unlimited number of systems, with pricing based on tiers that start at 10 systems and go up from there. We’ll work with your team to make sure we have the sizing correct!
Cloud native
Authorization
Entitlement Explosion Repair
Join Styra and PACLabs on April 11 for a webinar exploring how organizations are using Policy as Code for smarter Access Control.
Speak with an Engineer
Request time with our team to talk about how you can modernize your access management.