How to Enforce Fine-Grained Authorization in Microservices
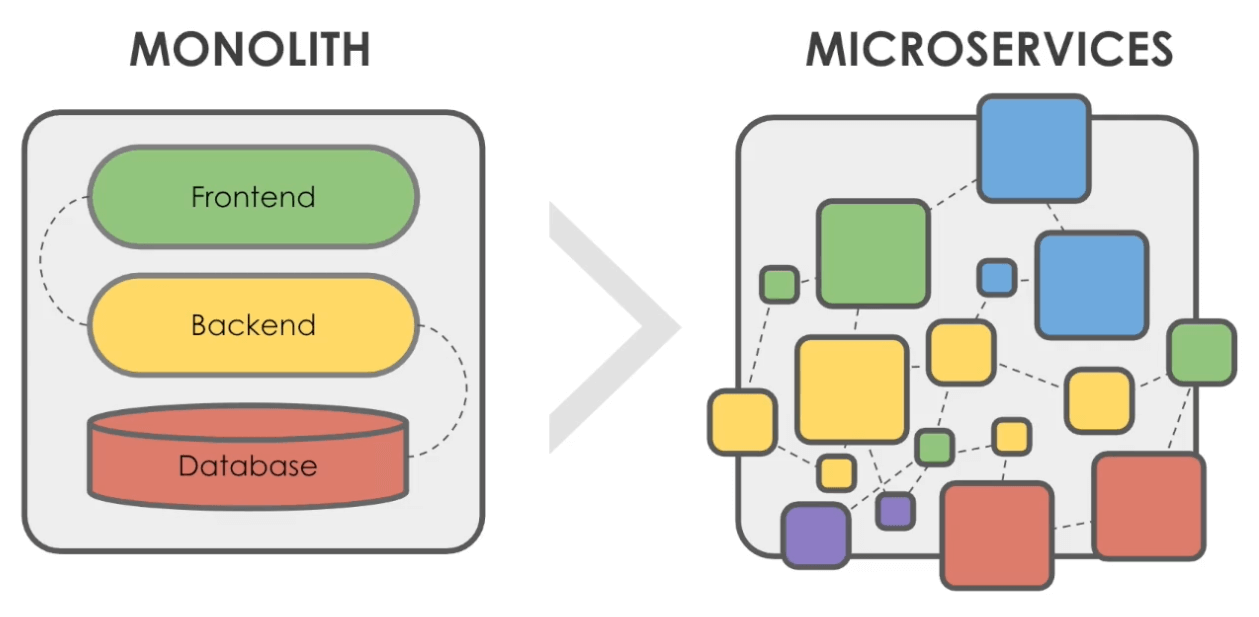
The shift from monolithic architectures to microservices poses complex authorization challenges to development teams. In this article, we look at how to enforce fine-grained access control in cloud-native environments as we make a case for a dynamic approach to authorization in microservices.
Key takeaways:
- Authorization is everywhere in microservice systems, increasing the need for fine-grained security at scale.
- Cloud-native development requires a more nuanced and dynamic approach to policy — through fine-grained authorization — to better support what is a highly distributed and often heterogeneous environment.
- Open Policy Agent (OPA) enables you to deliver fine-grained control at scale without compromising performance and speed of development.
Microservice Architecture Requires Fine-Grained Security at Scale
Microservices have become a widely adopted architecture for cloud-native application development. Companies like Netflix, Amazon and Spotify run their businesses on microservices architecture-based applications, so it’s no wonder this market is expected to register a 25.1% CAGR growth from 2021 to 2026, reaching $1.59 billion, according to a Technavio market analysis report.
This popularity is driven by the flexibility and scalability of microservices development.
The microservice architecture enables different development teams to build applications as a collection of small and independent services. In other words, these microservices can be developed (often using different languages and technologies), deployed, scaled, and upgraded independently. Different teams can own small independent services, which communicate with each other via APIs.
Source: Styra Academy
Deployment becomes agile and more resilient. If one microservice fails, the result can be degraded functionality rather than the crash of the entire system.
| Monolithic architecture | Microservice architecture |
| Few components (frontend, backend, database) | Several independent components, teams and technologies |
| Infrequent releases | Agile development |
Microservices projects are more complex because they:
- Involve different teams, often using a diversity of languages, technologies and tools to build new components.
- Add more authorization layers, as each microservice is a potential user that requires authorization when communicating with each other over APIs.
Simply put, authorization is about “who can do what” and “what can do what” in security. Microservices development, however, requires a more nuanced and dynamic approach to authorization, which can be better delivered through fine-grained access control.
What Is Fine-Grained Authorization in Microservices?
The amount of specificity involved in granting or denying access to resources makes fine-grained control more nuanced.
There’s more granularity, which means that a higher level of conditions is considered. For example, what if more microservices or teams are added to the architecture? What if temporary access is required? The coarse-grained authorization model can’t handle the level of flexibility required for highly scalable cloud-native architectures.
The Styra Academy offers a course on microservice authorization. Enroll for free now.
Microservice Authorization Challenges
Efficient fine-grained authorization is critical to minimizing risks and securing microservices from cyberattacks and misuse. Misconfiguration incidents can lead to onerous breaches. In fact, human error accounts for 95% of cybersecurity incidents, per the World Economic Forum’s The Global Risks Report 2022.
Authorization implementation challenges in microservices include:
- Enhanced compliance requires a global view of the policies across microservices. However, a centralized authorization system can add latency.
- The speed at which new teams are added, and the diversity of their tech stack, requires an agnostic approach for microservices.
Here’s where OPA can help you mitigate risks and accelerate development. You can minimize latency and still get a centralized authorization service by deploying a local authorization engine with each microservice. OPA is designed to be a general-purpose policy, which means it’s domain agnostic, too.
Why a Unified Approach to Fine-Grained Control across Microservices Is Best
Every time a microservice runs an API call on another microservice, an authorization policy must be enforced.
Having policies communicated in spreadsheets or wiki pages such as Confluence doesn’t work for dynamic development environments, such as microservices. This process hinders scalability and slows down development. In addition, audits become challenging when the knowledge and records are spread across services in multiple policy silos.
With OPA, you can decouple decision-making from enforcement — a more efficient way to orchestrate policies across your entire cloud-native environment.
So how does it work?
- The microservice hands the policy query to OPA.
- OPA makes a decision, returning the answer to the service.
- The service then has the responsibility to enforce the policy.
With Styra Declarative Application Services (DAS), policy decisions can be automated across your technology stack.
Styra DAS provides dynamic authorization as a control and management plane for OPA. Our unified approach to microservices authorization ensures fine-grained security thanks to the ability to incorporate real-time context in determining permissions and access. In fact, evaluating context is key to identifying and blocking lateral movement in case an asset is compromised.
With the industry pushing toward a zero-trust security model, enforcing fine-grained policies becomes more critical than ever. And Styra can help you scale this implementation process.
Deploy Styra DAS for Fine-Grained Authorization Solution
Styra DAS can evaluate real-time context against microservice policy authorization at scale for improved security, compliance and time to market. To see our fine-grained authorization solution in action, get started with Styra DAS Free now.
Frequently Asked Questions
What is authentication vs authorization in microservices?
Authentication verifies who a user/service is, while authorization identifies what type of access the user/service in question has been granted. To better understand the difference between authentication vs authorization in microservices, consider an API call. The microservice making the request needs to be authenticated first to confirm its identity. Then, it’s necessary to determine if it’s authorized to do what it’s asking.
What does fine-grained mean?
In authorization, fine-grained means that a higher level of specificity is taken into account when determining permissions to grant or deny access to data or applications.
What is fine-grained authorization with OAuth2?
Fine-grained authorization with OAuth2 protocol uses access tokens rather than credentials to identify and authorize access. To learn more about how to use OAuth 2.0 in OPA, read our blog post.
Read More:
How to Secure Kubernetes Cluster